The status of all websites mentioned are as reported at the time of writing.
At least 175 of nearly 700 government websites examined by Malaysiakini were considered “not secure”, which experts warned could lead to personal data breaches and other cybersecurity risks.
The audit by Malaysiakini was conducted between late May and early July on approximately 700 government websites that carry the domain name “.gov.my”.
These websites include but are not limited to, different ministries, agencies and departments at the federal and state levels, local councils, land offices and hospitals.
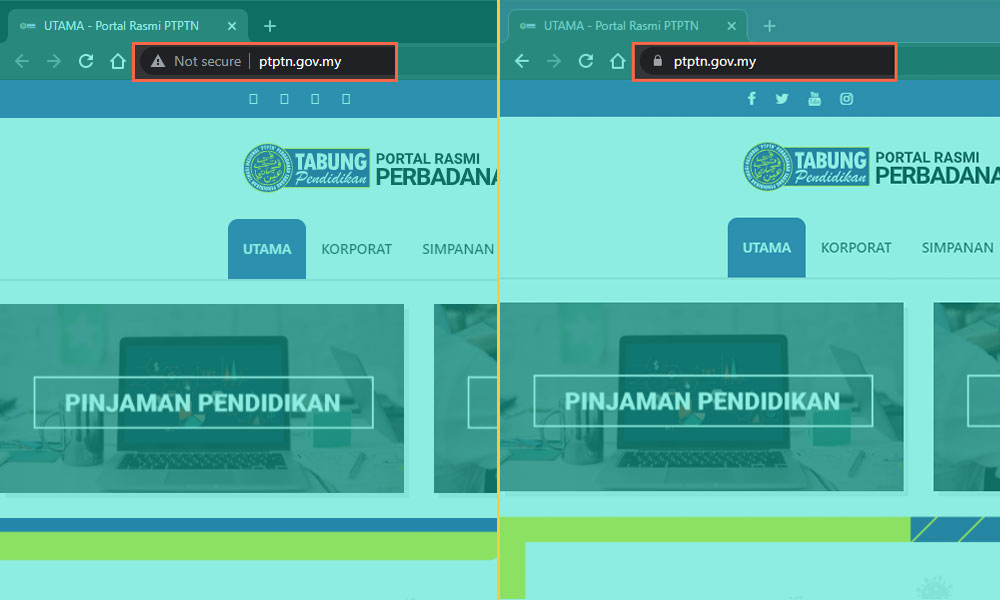
Websites are identified as “not secure” when the URL begins with “http” instead of “https”.
A “not secure” warning will be shown on the left side of the URL bar on a desktop computer web browser. A warning sign ⚠️ will be displayed instead on a smartphone.
There were 164 Hypertext Transfer Protocol (HTTP) government websites found to be “not secure” by major web browsers such as Chrome and Firefox. Another 11 Hypertext Transfer Protocol Secure (HTTPS) websites were deemed “secure” but were flagged for containing phishing attacks, spamware or other “malicious” activity.
The HTTP websites include the National Palace, Defence Ministry, and the Covid-19 Malaysia monitoring site.
Access to the Eastern Sabah Security Command (Esscom) website will prompt a privacy breach warning. A spokesperson for Esscom told Malaysiakini that the website is under maintenance and will be up and running by October.
When contacted, some government agencies and local authorities said that they are tightening the security of their website, including upgrading from HTTP to HTTPS.
255 HTTP websites were initially found on the list. 91 of them, including RTM, the Ceremonies and International Conferences Secretariat and the Public-Private Partnership Unit under the Prime Minister’s Department, and the Shah Alam City Council, upgraded to HTTPS soon after Malaysiakini contacted the respective authorities for comments.
Their responses are included in the table below.
A few websites in the table are malicious as they will try to install malware to a visitor’s device, while some contain spamware or a phishing attack.
| State | Name | HTTPS? | ||
|---|---|---|---|---|
| Federal | Anti-Doping Agency (Adamas) | |||
| Federal | Prime Minister's Department - Legal Affairs Division (BHEUU) | |||
| Federal | Cabinet Constitution and Intergovernmental Affairs Division (BKPP) | |||
| Federal | Prime Minister's Department - Property Management Division (BPH) | |||
| Federal | Prime Minister Office - Public Complaints Bureau (PCB) | |||
| Federal | Covid-19 Malaysia monitoring site | |||
| Federal | 15888 SMS Engine | |||
| Federal | Rehabilitasi Cheras Hospital | |||
| Federal | Sultan Ismail Hospital | |||
| Federal | Legal and Judicial Training Institute (ILKAP) |
As of Jul 15, 2021
It’s not secure without the ‘s’
All information sent from a user’s browser on an HTTP website is in text format.
However, information transmitted in HTTP is susceptible to interception.
“As a rule of thumb, it's generally not safe to submit information via a website that has been labelled ‘not secure’.
“This is especially true if the information is sensitive, like username, password, personal data and credit card data,” tech blogger Keith Rozario told Malaysiakini in an interview.
Some government websites were found to have sought sensitive information such as usernames, passwords, security phases, MyKad numbers, addresses and contact details through HTTP. [see box below]
HTTPS on the other hand, provides end-to-end encryption between a web browser and a server.
The information transmitted will be scrambled which can only be decrypted on either end.
Although hackers can still intercept data transmitted over the open internet, they will be getting unreadable texts.
For example, on the Chrome web browser, a “lock” symbol will be displayed to the left of the URL bar for HTTPS websites.
Malaysia Cyber Consumer Association chief activist Mohd Fazli Azran explained that HTTPS provides three layers of security - data encryption, data integrity and authentication.
What is sent from ’http’ and ‘https’ website?
Have a try
Feedback and login forms are ‘not secure’
There were over 100 HTTP government websites which asked for personal or login details when a user intended to submit feedback or file a complaint.
These included local council websites, such as Manjung Municipal Council and Kemaman Municipal Council.
Similarly, the websites of some federal agencies, such as the Legal Aid Department, Enforcement Agency Integrity Commission (EAIC) and the Legal Affairs Division (BHEUU) of the Prime Minister's Department, also did not have secure feedback or complaint forms.
Other services included tax payment portals such as the Johor e-Services, Bentong Municipal Council and the land and mines offices of Malacca and Terengganu.
The login page for internal systems on some websites, such as the salary and payslip inquiry system by the Melaka City Council and Dungun Municipal Council for their staff members, were not secure as well.
The National Higher Education Fund Corporation (PTPTN) had both its HTTP and HTTPS website co-exist at the same time, resulting in two nearly identical Skim Simpanan Pendidikan Nasional (SSPN) websites for its depositors. PTPTN has since rectified the issue by redirecting users on the HTTP website to its HTTPS site after it was contacted by Malaysiakini for a response.
Sometimes, a government website may have HTTPS on its main page but not on other pages within the website. For example, Sepang Municipal Council has an HTTPS main page but the HTTP form of the Sepang Local Youth Movement, which asked for plenty of personal information, was found “not secure”.
“It (the HTTP government website) could be illegitimate, it could be run by hackers. It could be malicious or someone can steal and manipulate your data,” explained cybersecurity senior consultant Razwan Mokhtar.
Static HTTP page can be harmful too
For most of the other HTTP websites gathered by Malaysiakini, their complaint or feedback forms are secure. For example, the Petaling Jaya City Council (MBPJ) had a safe complaint lodging and payment system despite its main page being flagged as “not secure”.
Meanwhile, most of the government departments and agencies, hospitals and some other local councils, would redirect users who wanted to submit feedback or lodge a complaint to the centralised Public Complaint Management System (SISPAA) which is secure.
The National Kenaf and Tobacco Board (LKTN) is a special case where both the HTTPS and HTTP forms can be found on its websites.
When contacted, spokespersons of some government agencies said that HTTPS is not required as they do not involve any transaction.
That said, it does not mean that web visitors are safe when on a static HTTP website that does not ask for personal information or involve money transactions.
A hacker could hack into the website and covertly inject malware into a website visitor’s computer. Known malware examples include cryptocurrency miners or users being redirected to a similar but malicious website for phishing attacks.
The video below provides examples explaining how a static HTTP website can be attacked or hijacked in many different ways.
Fazli said most of the static HTTP government websites are less harmful as they are not very attractive to hackers.
This is as malicious hackers know most users will not spend a long time on these websites, he elaborated.
However, he noted that there are chances the hackers may attack certain popular websites.
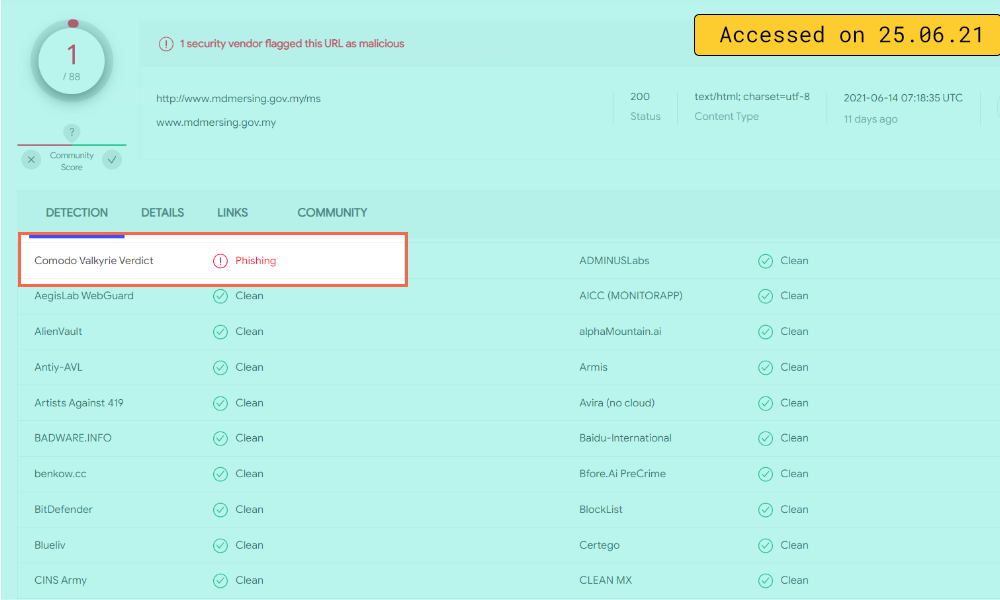
A check on all the HTTP websites that Malaysiakini gathered with VirusTotal, an online analysis tool for malware detection, flagged the Mersing District Council website for phishing attacks and the Shah Alam City Council website for spamware.
Meanwhile, the check results on most of the websites on Malaysiakini’s list showed that they were free from malicious malware and phishing attacks.
Is switching from HTTP to HTTPS an easy task?
Switching from HTTP to HTTPS cannot be done by just typing an "S" onto the URL.
Nonetheless, the process is “not hard”, according to Fazli.
What a website needs is to buy a valid Secure Sockets Layer (SSL) from an SSL certification provider and set up a web server configuration for the conversion, he explained.
Fazli also recommended the public to use the ‘HTTPS Everywhere’ browser extension that enhances browsing security by encrypting user communications with many major websites.
However, Razwan said that the conversion was not an easy task, especially since it involves hundreds of government websites.
He said that a huge online system usually takes five years to be developed from scratch and some systems may not belong to the respective government agencies.
As such, he hoped the public could understand the challenges of fixing the problem on a large scale.
“It is not a single website, it has a process to apply. The system belongs to the vendor, it does not belong to the government department.
“If a system belongs to a vendor, the government agency has to pass the request to change (from HTTP to HTTPS). If a server belongs to the government, they can get it done immediately,” said Razwan, who has experience in enhancing cybersecurity systems for the government in his 22-year career.
He added that the government agencies have to get the right security certification, especially the one certificated by the government, for their websites.
While noting the potential risk of visiting HTTP government websites, he interceded for the government, saying that it might be something the government had missed.
“Maybe this is something the government has overlooked, it is not aware of how critical it is,” he added.
HTTPS does not guarantee safety
That said, having HTTPS on a website’s domain doesn’t guarantee that it is safe. Among others, the portal of the Kelantan state government, Education Service Commission (SPP), and Alor Gajah Municipal Council were labelled “malicious” by VirusTotal despite being an HTTPS website.
The HTTPS portal of Perlis, Kedah and Pahang state governments, Pahang PAKR Rental Payment system, and Selayang Municipal Council contained spamware or phishing attacks.
When contacted, CyberSecurity Malaysia, an agency under the Communications and Multimedia Ministry, referred Malaysiakini to the Malaysian Administrative Modernisation and Management Planning Unit (Mampu) and National Cyber Security Agency (Nacsa).
Mampu is a unit placed under the Prime Minister’s Department tasked to digitalise and transform the public sector. Nacsa is an agency that belongs to the National Security Council (NSC). Nacsa is in charge of national cybersecurity matters.
Both Mampu and Nacsa did not reply to the questions posed by Malaysiakini in regard to the safety of the government websites.
Following the publication of this report, Malaysian Communications and Multimedia Commission (MCMC) chairperson Fadhlullah Suhaimi Abdul Malek said that the government will conduct a cybersecurity audit on the 175 government websites.
Communications and Multimedia Minister Saifuddin Abdullah also said the government has decided to make concerted efforts to tighten cybersecurity.

Advice to the public
Merely upgrading a website to HTTPS status is not the end of the story. Other measures can be used to determine its security level as pointed out by Fazli, who is also the former leader of the Open Web Application Security Project (OWASP) Malaysia Chapter.
Among others, the measures include setting up a firewall, user input sanitisation, strong password policy, two-factor authentication (2FA) or multi-factor authentication (MFA) and building a web application based on the OWASP Top 10 standard.
Besides upgrading the government websites to HTTPS status to boost public confidence, Fazli also advised the government to do routine security assessments on its websites.
He also called for a rightful amount of budget allocated for this purpose and to get help from an external security consultant company to review and improve the websites.
He suggested users who access government websites should verify their legitimacy and make sure that the SSL is in place if it asks for login or personal details.
Besides recommending users to equip their devices with antivirus software, he asked them to use the tools below to verify the safety of the websites.
As for Razwan, his advice is simple: For any website carrying a domain name without “https”, please do not go there.